Everything Else
How To: Use Google's New Privacy Tools to Stop Them from Tracking You
I'm sure everyone has heard about Google's changing privacy policy on March 1. It's scattered everywhere, with notification bubbles on Google Search, YouTube, and the rest of their products. Click here to see the new privacy policy that will take effect on March 1, 2012.

How To: Remain Anonymous and Chat Securely with Cryptocat
I'm sure we've all heard about MSN and Yahoo! Messenger, right? They can be useful, but the setup can be quite time consuming for those who need to use it just once or twice—and the privacy statements are a real bother. For example, we must provide our real details. You could use Fake Name Generator, but if you get caught, you will have your account suspended. I don't have a law degree, but to my understanding the United States recently passed legislation that gives the authorities the power ...

How To: Secure Your Computer with Norton DNS
There are so many hackers around these days, and they are becoming very smart. So smart that they have successfully taken down many government websites. The most recent attack was on the Department of Justice (DOJ). To read about the history of these hackers, check out Wikipedia.

How To: Keep Your Computer Organized in Windows 7
At some point, we all go from organized to disorganized. Let's assume you are a business executive working in a busy corporate building. Chances are you are going to get a heavy workload and it will impact how clean your workspace is. However, this article is about keeping your desktop clean and clutter free, along with the use of software to find documents you have misplaced.

How To: Find Out Who Unfriended You on Facebook
How many Facebook friends do you have? The average person on Facebook has around 140 friends while some hit the ridiculous Facebook friend limit of 5,000. Facebook states that its services are for people you know in person. I don't think anyone has 5,000 friends in person, do you? Personally, I don't even think Megan Fox has 5,000 friends in person, so how could any regular person have that many? But that's beside the point.

How To: Criminal Psychology - how stalkers and pedophiles can use the internet to track you
I want to write this article because in my childhood, I had experienced internet stalking which ultimately ended in physical stalking which then lead to several attempted abductions. I have now learned how to use the internet safely, who to communicate with and I've learned how stalkers work.

How To: A Basic Guide to Keeping Your Computer Clean & Running at Its Best Performance
Today's article serves as a general guide to keeping Windows 7 and Vista clean. The goal is to clean up your messy computer and have it running at maximum performance in no time. The question at hand is—what is your computer's performance like?

How To: Create a Partition in Windows 7
This tutorial will be based on creating a partition in Windows Seven. I have seen so many people attempt to do this themselves without guidance. Ultimately, they end up with a corrupt system. The aim of this tutorial is to make sure you don't corrupt your system.
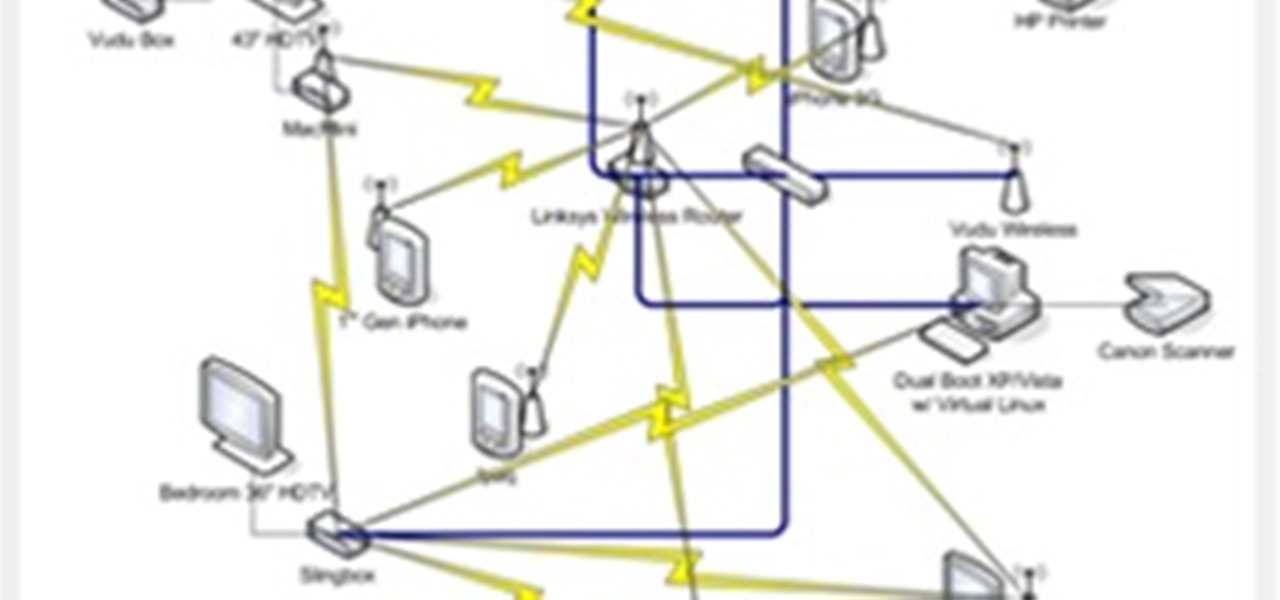
How To: Assign a Static IP Address in Windows 7
This article will be about setting up a static IP (Internet Protocol) address in Windows Seven. To see whether you should set one up, ask yourself the following: Do I have many computers in the house hold? Do I get connection issues often? Did you answer yes to both? Then you should set one up.

Hide Your Secrets: How to Password-Lock a Folder in Windows 7 with No Additional Software
Today's guide is on creating a password protected folder on Windows 7 without any additional software. Yes, you heard that right. No extra software at all! This guide is intended for beginners. But please note, this method should not be used to store financial or otherwise highly confidential material. It might be a good place to hide a planning document for a family member's birthday party or similar occasion where you need to keep something secret temporarily.

How To: Encrypt Your Sensitive Files Using TrueCrypt
Hello and welcome to another InfoSecurity World tutorial. The intent of this article is to teach one how to encrypt sensitive files. When set up correctly with a strong password, it would be almost impossible to hack. Even the FBI have had issues decrypting this software. I'm here to teach you how to create a general encrypted container—not the complex hidden TrueCrypt volume.

Lockdown: The InfoSecurity Guide to Securing Your Computer, Part II
This is Part II in the Lockdown: The InfoSecurity Guide To Securing Your Computer series. Before beginning, check out Part I. This article will cover using alternate software to increase your security and will provide you with some information about websites and programs that test a computer's security. It will also guide you to software you can install or follow so you know what programs need to be updated on the computer. Lastly, I will talk about some features that should be disabled when ...

Lockdown: The InfoSecurity Guide to Securing Your Computer, Part I
This is a two-part series to locking down the computer to provide maximum protection. Even though this guide will sound intrusive, we are talking about reality here. Extreme measures must be taken to protect our computers, especially when we have confidential documentation or do internet banking, which many people do. We all have to use electronic devices at some stage, whether it be for business or personal use.

The Anonymous Search Engine: How to Browse the Internet Without Being Tracked
How many people use the big search engines here? I'm going to estimate 90% of everyone on WonderHowto uses one of the following on a regular basis: Google, Bing or Yahoo! Search. The question is: are you in that 10%? You should seriously consider dumping Google search for DuckDuckGo. Why? DuckDuckGo does not track you.

How To: Permanently Erase Data So That It Cannot be Recovered
Today's tutorial will teach you how to erase data permanently so that it cannot be recovered. Many believe that having a file shredder on the computer means you are up to no good.

How To: Chrome Shares Your Activity with Google - Here's How to Use Comodo Dragon to Block It
Previously, we talked about how to secure Firefox. Today, we will talk about securing a Chromium based Browser. Why? Because Chrome recently beat Firefox in holding more customers.

How To: Install Windows 8 Beta on VirtualBox
Windows 8 Beta (Developer Preview) It wasn't that long ago Windows 7 was released - now Windows 8 Beta is here. I did do a Google search to see when the stable version will be out but wasn't able to find an official statement from Microsoft. However - I saw several articles on Google hinting that the final release might be in August or there about.

How To: Add Ctrl+Alt+Delete to Windows 7 Logon
Merry Christmas all! I hope you are all having a very wonderful day!

How To: Create Windows 7 GodMode
Hello and welcome to yet another InfoSecurity World tutorial. This post is based on the Windows 7 'GodMode' panel. Windows 7 comes with many hacks, cheats and tweaks. This bonus lesson will teach you how to create Windows 7 GodMode.

How To: amend Adobe Flash Settings
This article relates to changing the settings in Adobe Flash so that you can improve your overall computer security and privacy. Changing these settings might have a negative performance impact on your computer - but it is worth while.

How To: log on Windows 7 with username & password
The purpose of this article is to discuss how you can change your Windows 7 logon screen. This post will explain how to require a user to enter a username and password by default like the classic version of Windows.

How To: enable & disable Page File Encryption
Hello, welcome to my first post! Today, I would like to talk about setting up a Page File Encryption in Windows 7 and Vista. But first - what is a Page File Encryption? Why should you enable this option?


